Security teams do not just migrate a SIEM on a whim. They move because something has started to creak.
Often it begins with cost. Then performance. Then the slow realisation that onboarding new data sources feels heavier than it should. For many organisations running ArcSight, the conversation eventually turns to whether Elastic SIEM offers a cleaner, more flexible future.
Migration, though, is never just a technology decision. It is operational. Political. Financial. And if handled poorly, it quietly damages detection capability for months.
An ArcSight to Elastic SIEM migration checklist is not about ticking boxes. It is about preserving visibility while rebuilding the foundations underneath it.
Why Teams Move from Arcsight to Elastic

ArcSight has been in large enterprises for years. It is deeply embedded. Many SOC processes grew around it. That creates inertia.
But environments change and cloud adoption alters log patterns. Container workloads appear. Detection engineers want faster query cycles & analysts want cleaner dashboards.
Elastic enters the discussion because it handles large-scale ingestion well and offers more transparent scaling economics. Its search capability feels closer to modern data tooling than legacy SIEM interfaces. Detection engineering workflows tend to be quicker to iterate.
Still, none of that makes migration simple. The risk is not technical failure. The real risk is quiet degradation of coverage.
Before anything moves, clarity is required.
Establish What the Current SIEM is Really Doing
Most estates contain years of accumulated configuration. Correlation rules that no one remembers building. Parsers written by contractors long gone. Log feeds that were added during an audit panic and never reviewed again.
A sensible starting point is a capability baseline.
- Which log sources are ingested today.
- Which correlation rules still generate meaningful alerts.
- Which dashboards are actively used.
- What compliance reports depend on the platform.
This is not an inventory exercise for its own sake. It prevents a common mistake. Rebuilding everything out of habit.
Some ArcSight rules may no longer be relevant. Some may be overly complex and can be simplified in Elastic. Others may be critical and must be ported precisely.
The ArcSight to Elastic SIEM migration checklist should begin with understanding operational reality rather than architecture diagrams.
Architecture Design Before Ingestion
Elastic can be deployed in different ways. Self-managed clusters. Cloud-hosted options. Hybrid models. Each choice affects data flow, retention strategy and cost structure.
A migration is an opportunity to correct architectural shortcuts made years earlier. Log retention policies may need revision. Cold storage tiers might become viable. Ingestion pipelines can be simplified.
Capacity planning needs sober assessment. Historic ingestion rates from ArcSight provide a baseline, but growth projections must reflect new data types such as container logs, SaaS audit feeds or endpoint telemetry expansion.
Design decisions taken here shape everything downstream. If storage tiers are misjudged, performance suffers. If network routing is overlooked, ingestion becomes unstable.
Moving tools without redesigning structure only relocates existing friction.
Mapping Data Sources and Parsers
Log normalisation is rarely glamorous. It is also where migrations succeed or fail.
ArcSight connectors often include custom parsing logic. Some organisations rely heavily on device-specific content packs. Others have years of bespoke field mappings tied to internal processes.
Elastic uses its own ingestion pipelines and mappings. Field naming conventions differ. Correlation logic may depend on different field structures.
A detailed mapping exercise is necessary:
• Source log type
• Current ArcSight parser behaviour
• Target Elastic ingestion method
• Field equivalence and gaps
Not every field requires replication. Some may never be used. Others are critical for detection logic or compliance reporting.
This phase exposes hidden dependencies. It also uncovers redundant log feeds that can be retired rather than migrated.
Rebuilding Detection Logic
Correlation rules in ArcSight do not transfer automatically. They must be rewritten in Elastic’s detection framework.
This is where migration becomes more than translation. It becomes refinement.
Some legacy rules may be noisy and tolerated only because analysts are used to them. Elastic provides an opportunity to adjust thresholds, redesign logic or combine multiple detections into cleaner workflows.
However, any change carries risk. Blindly “improving” rules during migration can reduce coverage.
Parallel testing is essential. Run both SIEMs side by side for a defined period. Compare alert outputs. Measure variance. Investigate gaps.
Detection engineering teams often discover that the process improves overall signal quality. But that outcome depends on disciplined testing rather than optimism.
A Practical Migration Flow
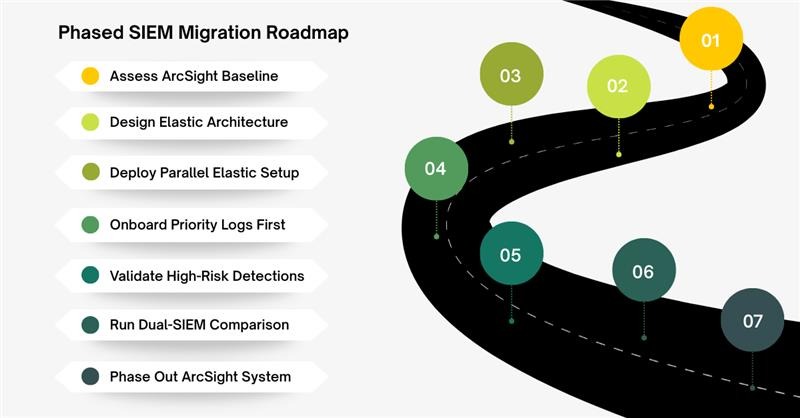
The sequence below represents a stable path observed in several enterprise transitions.
- Baseline existing ArcSight capabilities
- Design Elastic architecture and retention model
- Stand up parallel Elastic environment
- Onboard priority log sources first
- Rebuild and validate high-risk detection rules
- Run dual-SIEM comparison period
- Decommission ArcSight in phased stages
This sequence avoids abrupt cutovers. It allows operational confidence to build gradually.
Some organisations attempt a “big bang” migration. It looks efficient on paper. In practice, it introduces blind spots at the worst possible moment.
Parallel operation costs more temporarily. It reduces long-term damage.
Compliance and Reporting Continuity
Many enterprises depend on SIEM outputs for audit evidence. PCI reporting. ISO logs. Internal governance metrics.
These reports are often tightly coupled to ArcSight dashboards and export formats.
During migration planning, compliance stakeholders must be consulted early. Waiting until decommissioning reveals missing artefacts invites regulatory discomfort. This becomes even more critical for organizations that store large volumes of customer interaction and sales data inside CRM systems, where continuous CRM security monitoring and managed security services help maintain audit readiness.
Elastic reporting capabilities differ. They may need redesign rather than replication.
A review of mandatory reporting requirements ensures nothing essential disappears during the transition.
Operational Readiness and SOC Impact
Technology migrations affect people more than systems.
SOC analysts who have used ArcSight for years build instinctive navigation habits. Query syntax becomes muscle memory. Alert triage workflows become second nature.
Elastic introduces different query structures and visualisation methods. Without structured onboarding, productivity dips.
Training must be timed carefully. Too early and knowledge fades before go-live. Too late and analysts struggle during the dual-running phase.
Playbooks should be updated gradually during parallel operations. This avoids a sudden procedural rewrite on cutover day.
A SIEM migration is not successful if detection improves but analyst efficiency collapses.
Data Retention and Cost Modelling
Cost transparency often motivates migration in the first place.
ArcSight licensing models can feel opaque at scale. Elastic’s model, while more flexible, still requires disciplined monitoring.
Retention strategy influences storage cost significantly. Hot versus warm tiers. Indexed data versus archived logs. Snapshot frequency.
Without a clear financial model, teams risk recreating the same budgeting pressure they hoped to escape.
The ArcSight to Elastic SIEM migration checklist should therefore include projected ingestion growth, storage tier distribution, and review cadence for cost oversight.
Migration without financial clarity becomes a temporary relief rather than a sustainable solution.
Risk Management and Rollback Planning
Every major platform transition carries operational risk.
Unexpected parser failures. Detection mismatches. Performance bottlenecks under real load.
A rollback plan is rarely discussed openly, but it should exist. During the parallel phase, ArcSight should remain capable of handling full production ingestion until Elastic demonstrates stability.
Rollback criteria must be defined in advance. Not emotionally decided during an outage.
This discipline reduces pressure during go-live. It also reassures stakeholders who may be wary of change.
Conclusion
An ArcSight to Elastic SIEM migration checklist is not a document to satisfy procurement. It is a structured safeguard against degraded visibility.
When done carefully, migration modernises detection engineering, improves scalability and aligns cost with growth. When rushed, it introduces silent risk.
The difference lies in preparation. Baseline honestly. Design deliberately. Validate rigorously.
CyberNX can help you navigate this transition. Their team of experts can engage deeply with you to understand your business objectives, current infrastructure & challenges. And they implement strong monitoring mechanisms for proactive detection and mitigation of emerging threats.
Changing SIEM platforms is a major change. It deserves steady hands rather than hurried execution.




%201.png)

%201.png)

%201.png)