Compliance has shifted. It no longer sits in a policy folder waiting for an annual audit. It lives inside daily operations. Security teams feel this most sharply when regulators ask for evidence that cannot be reconstructed after the fact.
Logs must be complete. Alerts must be traceable. Access must be provable. And the controls must stand up to scrutiny months later.
This is where CrowdStrike NG-SIEM for compliance enters the conversation. Not as another dashboard, but as an operational shift in how evidence is collected, correlated and preserved. It changes how teams think about visibility and control, particularly in environments where audit pressure never really fades.
Compliance is No Longer a Paperwork Problem
Frameworks such as ISO 27001, PCI DSS, DORA, and sector-specific regulations increasingly expect continuous monitoring. Auditors want to see that controls are active, not just documented.
The difficulty rarely sits with defining the controls. It sits with proving them. Traditional SIEM deployments often struggle here. Data gaps appear. Logs are dropped due to storage limits. Alert tuning becomes inconsistent. Six months later, reconstructing events becomes guesswork.
Security teams often compensate with manual effort. Spreadsheets grow. Evidence packs become heavier each year. Meanwhile, adversaries do not slow down to accommodate audit cycles.
CrowdStrike NG-SIEM for compliance changes the structure of this problem. By combining endpoint telemetry from the CrowdStrike Falcon platform with broader log ingestion, it reduces the separation between detection and audit evidence. What is investigated operationally can also be retained defensibly.
That link matters more than many realise.
The Architectural Shift Behind NG-SIEM

Traditional SIEM tools were designed around log aggregation first. Detection logic came later. Storage costs shaped retention decisions. Scaling meant infrastructure expansion.
NG-SIEM, as delivered within the CrowdStrike Falcon platform ecosystem, approaches the problem differently. Endpoint telemetry is already high fidelity and structured. Extending this data into centralised correlation reduces reliance on third-party parsing and fragile connectors.
The effect is subtle but significant.
Instead of pulling together disjointed evidence during an audit, teams can demonstrate:
- Consistent data collection across endpoints
- Real-time correlation of suspicious behaviour
- Integrated response records
- Immutable retention policies
Compliance stops being a separate activity and becomes an output of operational security.
There is still configuration work involved. No platform removes that. But the baseline is stronger.
Where Compliance Requirements Meet Operational Reality
Consider what auditors typically ask for:
- Log retention evidence
- Privileged access monitoring
- Incident response traceability
- Change management validation
- Proof of continuous monitoring
These requests sound straightforward until they intersect with complex hybrid estates. Cloud workloads generate one set of logs. Endpoints another. Identity systems another still. Pulling them together consistently is rarely smooth.
CrowdStrike NG-SIEM for compliance addresses this by anchoring correlation at the endpoint level while extending visibility into cloud, identity and network layers. The endpoint becomes a reliable source of truth rather than just another log feed.
There is a practical advantage here. Endpoint telemetry is harder for attackers to manipulate without detection. For compliance teams, that strengthens evidentiary confidence.
A Closer Look at How NG-SIEM Supports Audit Defensibility
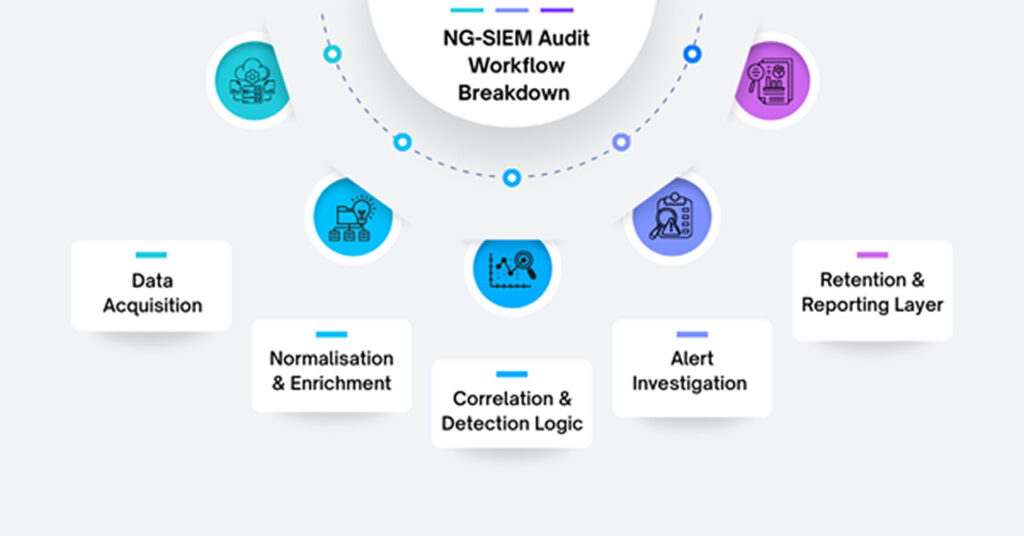
Before diving into specifics, it helps to break down how the workflow aligns with regulatory expectations.
1. Data Acquisition
Endpoint and cloud telemetry collected continuously.
2. Normalisation and Enrichment
Events contextualised with user, device and threat intelligence data.
3. Correlation and Detection Logic
Behavioural analysis applied in near real time.
4. Alert Investigation and Response Tracking
Actions recorded, timelines preserved.
5. Retention and Reporting Layer
Searchable, exportable records aligned with compliance frameworks.
Each stage reinforces the next. Evidence is not generated after the event. It accumulates naturally as part of daily monitoring.
The compliance benefit lies in continuity. Controls operate visibly. Investigations leave structured traces. Reports are drawn from live systems rather than reconstructed archives.
Reducing Blind Spots Without Inflating Cost
A frequent concern with SIEM expansion is cost. Log ingestion pricing has historically forced difficult decisions about what to retain and for how long.
When retention periods are driven by budget rather than regulation, compliance risk creeps in quietly.
CrowdStrike NG-SIEM for compliance attempts to address this by leveraging its cloud-native architecture. Storage scalability becomes less of a physical constraint. More importantly, high-value telemetry originates from the Falcon sensor, reducing the need to ingest redundant low-signal logs.
This does not eliminate cost considerations. It does shift them. Organisations can align retention more closely with regulatory obligations rather than arbitrary limits imposed by infrastructure.
Over time, that alignment simplifies audit preparation.
Bridging SecOps and GRC Teams
In many organisations, security operations and GRC teams operate in parallel. They meet during audits, exchange evidence, then separate again.
That division creates friction. Operations teams optimise for detection speed. Governance teams optimise for documentation quality.
CrowdStrike NG-SIEM narrows that divide because detection workflows and compliance artefacts draw from the same data foundation. An investigated alert already contains much of the evidence an auditor would later request.
This does not remove the need for policy mapping. Controls still need to be aligned to frameworks. But the raw material becomes consistent.
There is also a cultural shift. When operational data directly supports compliance, security teams gain clearer visibility into why thorough logging and structured response matters beyond incident containment.
Real-world Pressures Shaping Adoption

Regulators increasingly examine not just whether controls exist, but how quickly incidents are detected and contained. Response timelines appear in audit conversations more often than before.
High-profile breaches across financial services and critical infrastructure have reinforced this scrutiny. Public reporting obligations intensify the pressure. Delayed detection is no longer viewed as a technical oversight. It becomes a governance failure.
In that climate, organisations reassess whether legacy SIEM deployments truly support modern IT regulatory compliance demands across hybrid and cloud environments.
CrowdStrike NG-SIEM for Compliance aligns with this reassessment by combining behavioural detection with searchable historical depth. When incidents occur, teams can demonstrate:
- When activity began
- When it was detected
- What actions followed
- Whether containment succeeded
That chain of evidence carries weight in regulatory reviews.
Migration Considerations
Adopting NG-SIEM is rarely a simple replacement exercise. Existing log pipelines, integrations and reporting tools must be evaluated carefully.
Some organisations retain elements of their legacy SIEM for niche use cases. Others consolidate fully into the Falcon ecosystem. The decision often depends on data volume, contractual obligations and internal expertise.
It is also important to assess detection maturity before migration. Technology alone does not produce compliance. Alert tuning, access governance and response discipline remain critical.
CrowdStrike NG-SIEM for Compliance strengthens the foundation. It does not substitute governance processes. Teams that recognise this tend to achieve better outcomes.
Long-term Implications for Regulated Industries
Financial services, healthcare and critical national infrastructure face escalating oversight. Data sovereignty questions complicate cloud adoption. Cross-border reporting requirements introduce additional layers of complexity.
A cloud-native SIEM with strong endpoint telemetry simplifies part of this landscape, particularly where remote and hybrid working patterns persist.
Compliance evidence must follow users across devices and locations. Endpoint-anchored telemetry supports that mobility. Traditional perimeter-based logging models struggle here.
The shift is gradual, but noticeable. Organisations moving toward NG-SIEM models often report smoother audit cycles after the first full reporting period. Preparation time decreases because data retrieval becomes routine rather than reactive.
The impact compounds over time.
Conclusion
Using CrowdStrike NG-SIEM for compliance represents more than just adopting a new logging platform. It reflects an operational convergence between detection and defensibility. In environments where regulators expect continuous assurance, that convergence carries strategic weight.
The technology does not remove the need for governance discipline or clear policy mapping. It does, however, reduce fragmentation between security monitoring and audit evidence. For many organisations, that alone justifies serious evaluation.
Deciding whether it aligns with existing architecture, regulatory exposure and operational maturity requires careful assessment. CyberNX is a reliable and trusted CrowdStrike partner and can help you with CrowdStrike consulting. They can help you stream Falcon data with AI-driven SIEM and accelerate SOC efficiency, reduce noise and enable smarter threat response.
The value emerges over time. Quietly. In fewer audit surprises and clearer visibility when scrutiny arrives.




%201.png)

%201.png)

%201.png)

